
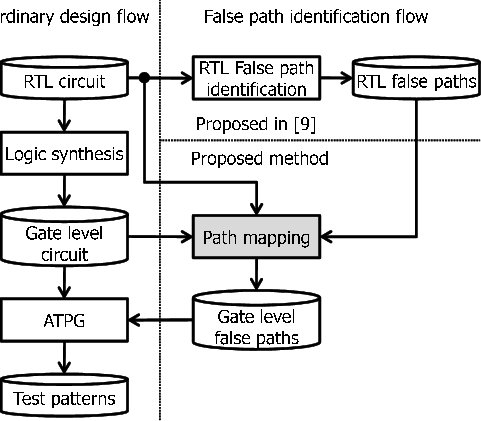
Verification is an important part of the Electronic Design Automation (EDA) design flow which currently takes a considerable amount of time. During the synthesis process, Different optimizations are done to the Register-Transfer-Level (RTL) code to optimize the power, area, and speed of the circuit. These optimizations result in changes in the names of signals at the gate level. Automatic signal mapping can improve the verification process and can be used to guide functional verification activities between the two presentations using (Clock domain crossing (CDC) analysis in RTL, Gate Level CDC
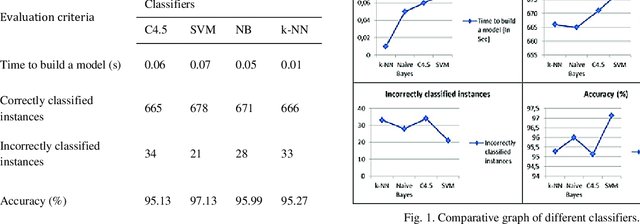
There are many cancer patients, especially breast cancer patients as it is the most common type of cancer. Due to the huge number of breast cancer patients, many breast cancer-focused hospitals aren't able to process the huge number of patients and might expose some women to late stages of cancer. Thus, the automation of the process can help these hospitals in speeding up the process of cancer detection. In this paper, the authors test several machine learning models such as k-nearest neighbours (KNN), support vector machine (SVM), and artificial neural network (ANN). They then compare their
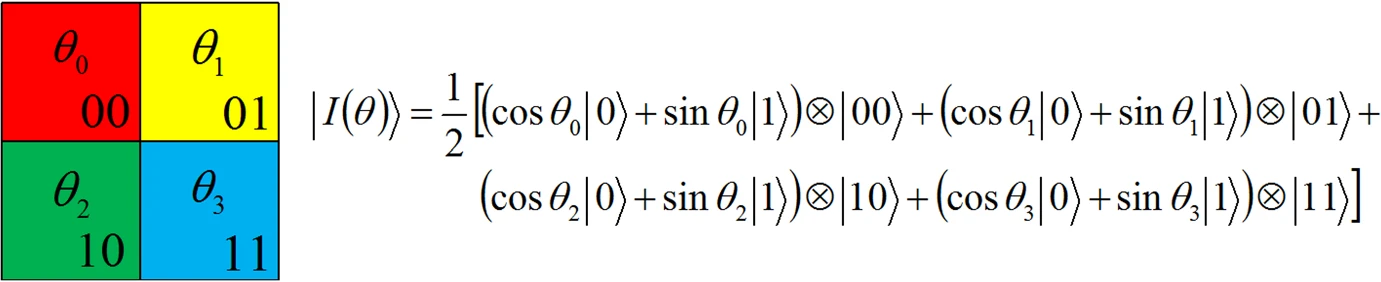
We present QIRHSI, a novel quantum image representation method based on the HSI color space model. QIRHSI integrates the advantages of the Flexible Representation of Quantum Images (FRQI) model and the Novel Enhanced Quantum Representation (NEQR) model. On the one hand, the proposed QIRHSI model is better suited for the image processing related to intensity information via binary qubit sequence than multi-channel representation for quantum image (MCQI) (multi-channel FRQI). On the other hand, the QIRHSI model requires less storage space (10 qubits) in the hue and saturation channels, compared
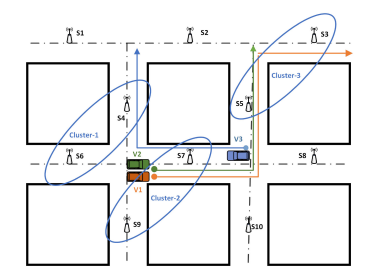
This work proposes novel proactive caching schemes for minimizing the communication latency in Vehicular Ad Hoc Networks (VANETs) under freeway and city mobility models. The main philosophy that underlies these schemes is to exploit information that may be available a priori for vehicles' demands and mobility patterns. We consider two paradigms: cooperative, wherein multiple Roadside Units (RSUs) collaborate to expedite the transfer of information to the intended user, and non-cooperative, wherein each RSU operates independently of other RSUs in the network. To develop the proposed schemes
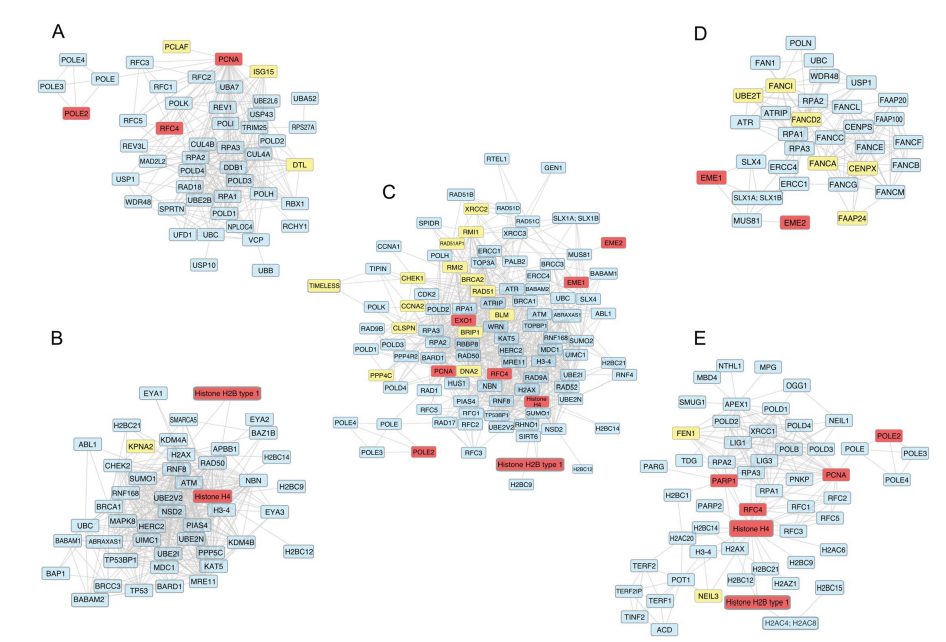
In the era of precision medicine, analyzing the transcriptomic profile of patients is essential to tailor the appropriate therapy. In this study, we explored transcriptional differences between two invasive breast cancer subtypes; infiltrating ductal carcinoma (IDC) and lobular carcinoma (LC) using RNA-Seq data deposited in the TCGA-BRCA project. We revealed 3854 differentially expressed genes between normal ductal tissues and IDC. In addition, IDC to LC comparison resulted in 663 differentially expressed genes. We then focused on DNA repair genes because of their known effects on patients'
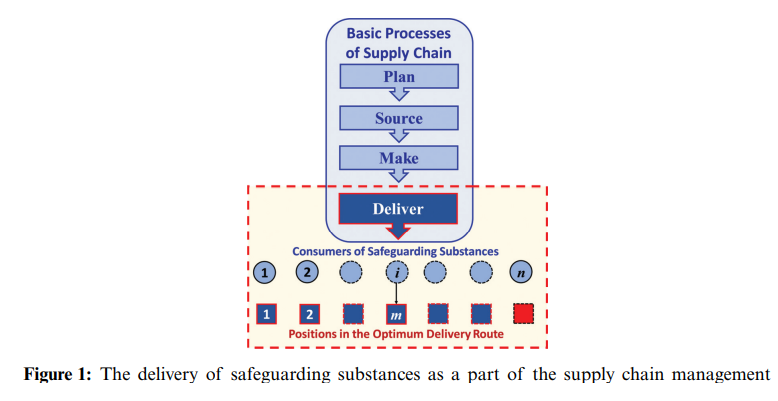
The optimum delivery of safeguarding substances is a major part of supply chain management and a crucial issue in the mitigation against the outbreak of pandemics. A problem arises for a decision maker who wants to optimally choose a subset of candidate consumers to maximize the distributed quantities of the needed safeguarding substances within a specic time period. A nonlinear binary mathematical programming model for the problem is formulated. The decision variables are binary ones that represent whether to choose a specic consumer, and design constraints are formulated to keep track of the
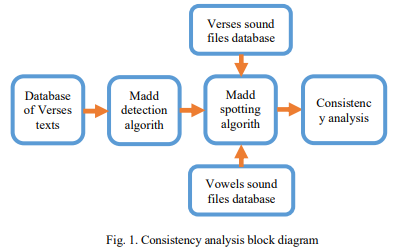
A consistency analysis is performed for one of the famous Tajweed rules in the Holy Quran - Madd rules. They are tested on records of one of the famous reference reciters - Sheikh El-Hosary-to find a consistent boundaries and to evaluate the performance of other new learners. A vowel detection algorithm is used to detect the duration of the detected Madd patterns. This algorithm was applied on a dataset of 105 minutes of Quranic records of Sheikh El-Hosary. The consistency result is found to be normally distributed with a mean of 0.379 second of one movement time of Madd and standard deviation
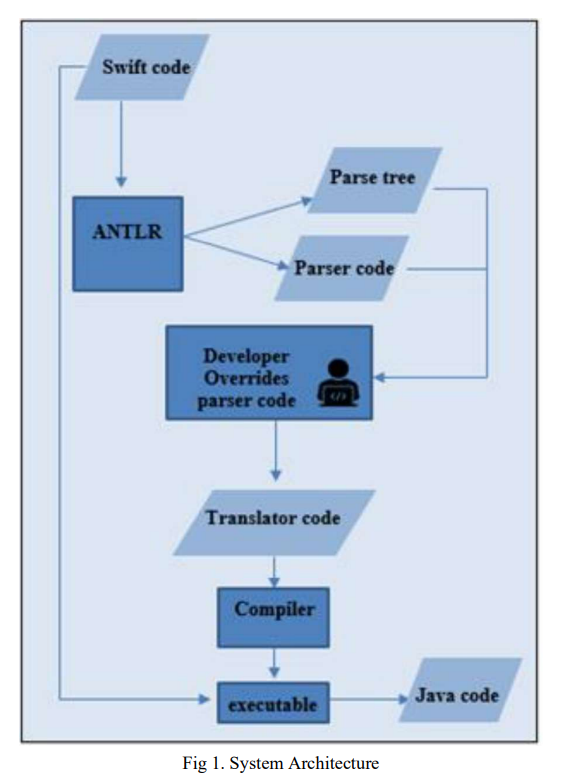
Numerous commercial tools like Xamarin, React Native and PhoneGap utilize the concept of cross-platform mobile applications development that builds applications once and runs it everywhere opposed to native mobile app development that writes in a specific programming language for every platform. These commercial tools are not very efficient for native developers as mobile applications must be written in specific language and they need the usage of specific frameworks. In this paper, a suggested approach in TCAIOSC tool to convert mobile applications from Android to iOS is used to develop the
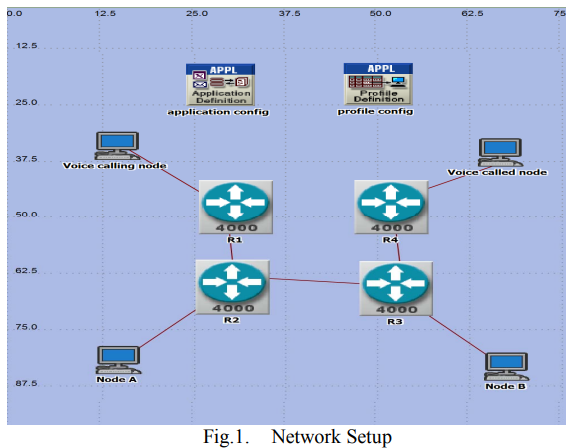
IPv4 address space is exhausted. Internet Engineering Task Force (IETF) developed IPv6 -the upgrade of IPv4- to satisfy the continual increase of the IP address needs. The Internet is so ramified and enormous that the complete transition from IPv4 to IPv6 is slow. Therefore, their coexistence is inevitable. Manually configured tunnels are an important solution to allow this co-existence that allows transmitting native IPv6 packets over IPv4 networks. Meanwhile, VoIP is also gaining momentum with expectation to occupy considerable percentage of Internet traffic. In this paper, we compare the
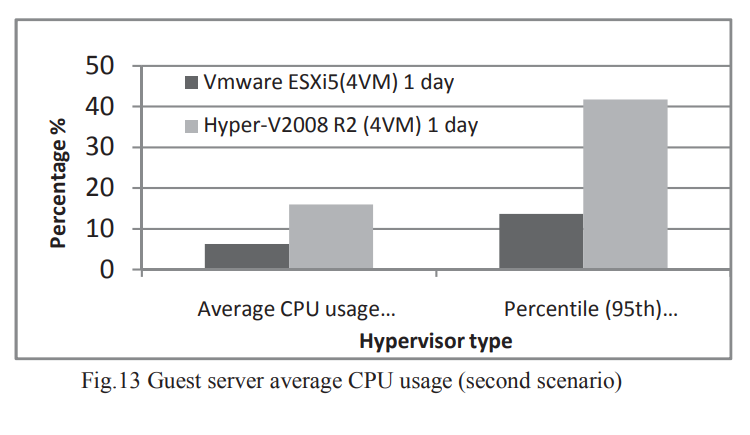
The virtualization of IT infrastructure enables the consolidation and pooling of IT resources so that they can be shared over diverse applications to offset the limitation of shrinking resources and growing business needs. It provides a logical abstraction of physical computing resources and creates computing environments that are not restricted by physical configuration or implementation. Virtualization is very important for cloud computing because the delivery of services is simplified by providing a platform for optimizing complex IT resources in a scalable manner, which makes cloud