Breadcrumb

Software and Communications
Features selection for building an early diagnosis machine learning model for Parkinson's disease
In this work, different approaches were evaluated to optimize building machine learning classification models for the early diagnosis of the Parkinson disease. The goal was to sort the medical measurements and select the most relevant parameters to build a faster and more accurate model using feature selection techniques. Decreasing the number of features to build a model could lead to more efficient machine learning algorithm and help doctors to focus on what are the most important measurements to take into account. For feature selection we compared the Filter and Wrapper techniques. Then we
Combined regional and spatio-temporal approach improves hepatic tumors classification in Multiphase CT
In this work, we investigate the effect of using spatio-tepmoral features on a regional basis on the liver focal lesions classification performance in the multiphase CT images. Texture, Density, and temporal feature set and their different combinations along spatial partitioned ROI were investigated to better characterizing five hepatic pathologies from multiphase contrast-enhanced CT scans. Embedded feature selection followed by decision tree ensembles classification with ten folds cross-validation were employed to classify a total of 180 ROI includes normal tissues, cyst, haemangioma
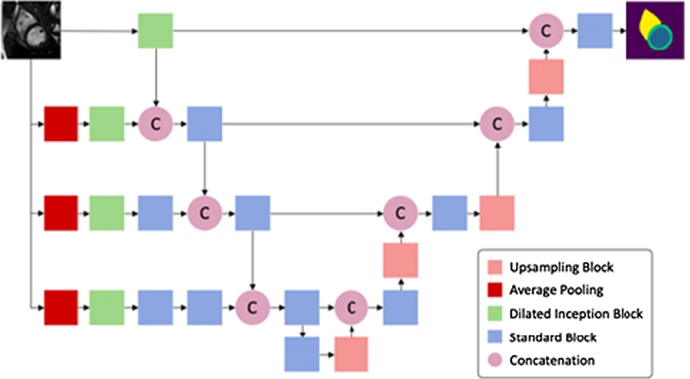
Multi-center, Multi-vendor, and Multi-disease Cardiac Image Segmentation Using Scale-Independent Multi-gate UNET
Heart segmentation in Cardiac MRI images is a fundamental step to quantify myocardium global function. In this paper, we introduce a pipeline for heart localization and segmentation that is fast and robust even in the apical slices that have small myocardium. Also, we propose an enhancement to the popular U-Net architecture for segmentation. The proposed method utilizes the aggregation of different feature scales from the image by using the inception block along with the multi-gate block that propagates the multi-scale context of the supplied data where the heart is subject to changes in scale
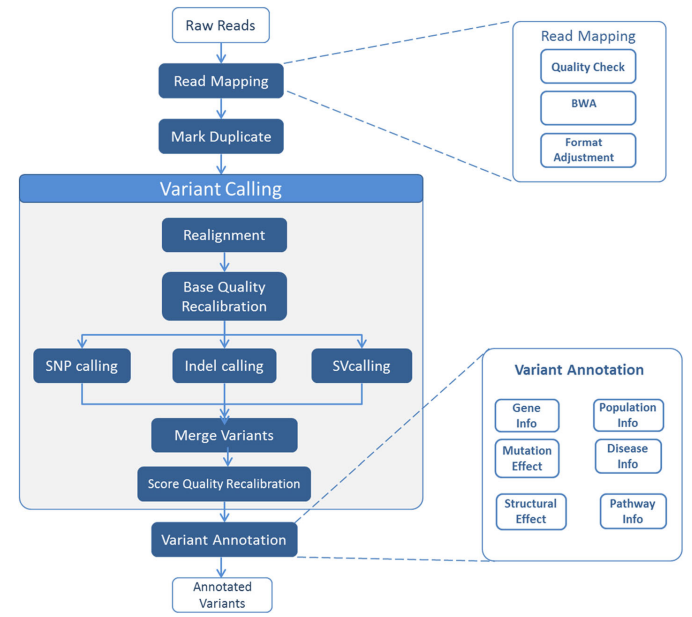
MC-GenomeKey: A multicloud system for the detection and annotation of genomic variants
Health Records Privacy Issues in Cloud Computing
Personal health record service avail patients to store and dominate their healthy information data through the cloud. Many users like medical doctors, health care providers and family members can access this data through the internet. However, there are privacy issues related to data exposure and data breaches, causing risk to patients' lives. Encryption techniques like public key encryption are applied but they are not efficient and very complex, in addition to scalability problems. In this paper, various multi-authority attributes based on encryption solutions features are discussed that

A survey on smart cities’ IoT
The rise of the Internet of Things (IoT) has led to a numerous and diverse amount of products and real life implementations for smart cities in the last few years. With the many opportunities and challenges, the academic and industrial field has come up with many hardware and middleware platforms. We categorise these different IoT applications and solutions into different domains and present an application for each. This survey aims at defining the state-of-the-art major and common technologies, frameworks, and applications used to open doors to drive future research and to spark new ideas for
Traffisense: A smart integrated visual sensing system for traffic monitoring
Intelligent camera systems provide an effective solution for road traffic monitoring with traffic stream characteristics, such as volumes and densities, continuously computed and relayed to control stations. However, developing a functional vision-based traffic monitoring system is a complex task that entails the creation of appropriate visual sensing platforms with on-board visual analytics algorithms, integration of versatile technologies for data provision and stream management, and development of data visualization techniques suitable for end-users. This paper describes TraffiSense, a
Towards IT-Legal Framework for Cloud Computing
As the common understanding of Cloud Computing is continuously evolving, the terminology and concepts used to define it often need clarifying. Therefore, Cloud customers and Cloud Providers are used to dispute about Service Level Agreements, Service Level Objectives and Quality of Service. Simultaneously, SLAs/SLOs/QoS represent other related technical problems such as Security, Privacy, Compliancy and others. Technical problems are usually defined within technical context, where both parties ignore analyzing problem's legally related causes. In fact, these problems are stemming from the
Transform domain two dimensional and diagonal modular principal component analysis for facial recognition employing different windowing techniques
Spatial domain facial recognition Modular IMage Principal Component Analysis (MIMPCA) has an improved recognition rate compared to the conventional PCA. In the MPCA, face images are divided into smaller sub-images and the PCA approach is applied to each of these sub-images. In this work, the Transform Domain implementation of MPCA is presented. The facial image has two representations. The Two Dimensional MPCA (TD-2D-MPCA) and the Diagonal matrix MPCA (TD-Dia-MPCA). The sub-images are processed using both non-overlapping and overlapping windows. All the test results, for noise free and noisy
Towards Efficient Online Topic Detection through Automated Bursty Feature Detection from Arabic Twitter Streams
Detecting trending topics or events from Twitter is an active research area. The first step in detecting such topics focuses on efficiently capturing textual features that exhibit an unusual high rate of appearance during a specific timeframe. Previous work in this area has resulted in coining the term "detecting bursty features" to refer to this step. In this paper, TFIDF, entropy, and stream chunking are adapted to investigate a new technique for detecting bursty features from an Arabic Twitter stream. Experimental results comparing bursty features extracted from Twitter streams, to Twitter