
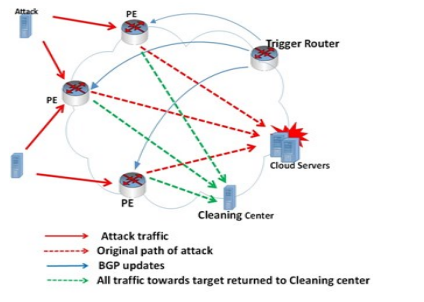
Greater portions of the world are moving to cloud computing because of its advantages However, due to its distributed nature, it can be easily exploited by Distributed Denial of Service (DDoS) attacks. In distributed DDoS attacks, legitimate users are prevented from using cloud resources. In this paper, the various DDoS detection and defenses mechanisms cloud computing are reviewed. We propose a new technique based on Remote Triggered Black Hole (RTBH) to prevent DDoS attacks before it target to cloud resources. © 2018 IEEE.
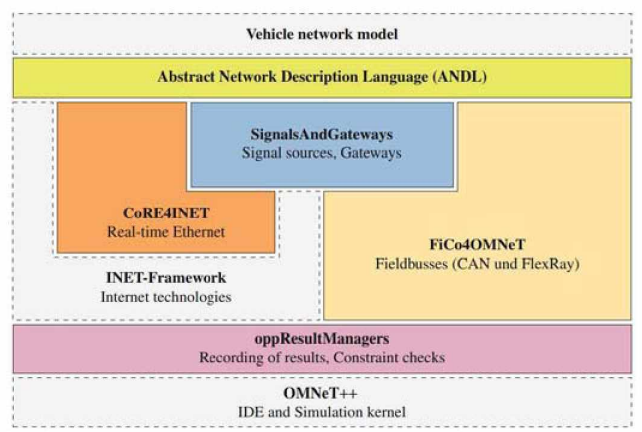
In the last decade, Ethernet networks that require real time constraints are massively increased. Switched Ethernet is reshaping in-vehicle communications. To meet real-time requirements for diverse data types in automotive communications, Quality-of-Service protocols that go beyond the mere use of priorities are required. In Vehicle networks requirements are evolving and need better Quality-of-Service (QoS) options. This applies also for industrial networks implementation. Time Sensitive Networking (TSN) IEEE 802.1 Task working group are providing wide variety of Standard. This standard
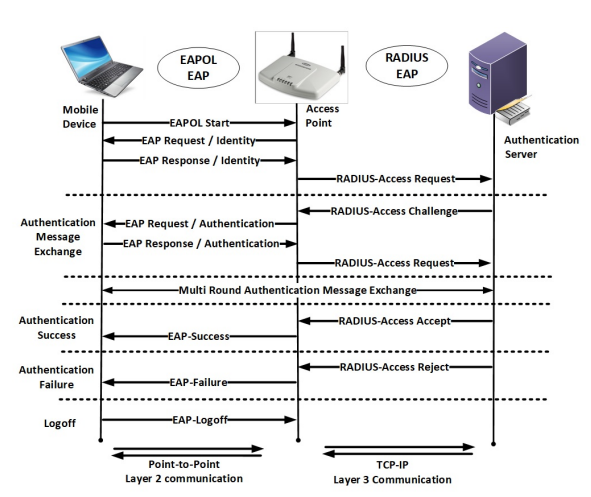
Organizations and network developers continuously exert much money and efforts to secure wireless transmission. WPA2 framework is widely deployed for Wi-Fi communications since it is efficient and secure against several wireless attacks. However, WPA2 security has been lately threatened by advanced developed versions of wireless attacks. The increase of computer processing power, continuous efforts by penetration testers, network evaluators and researchers led to the emerging of new advanced attacking techniques that may exploit WPA2 wireless systems detected vulnerabilities. In this paper, we
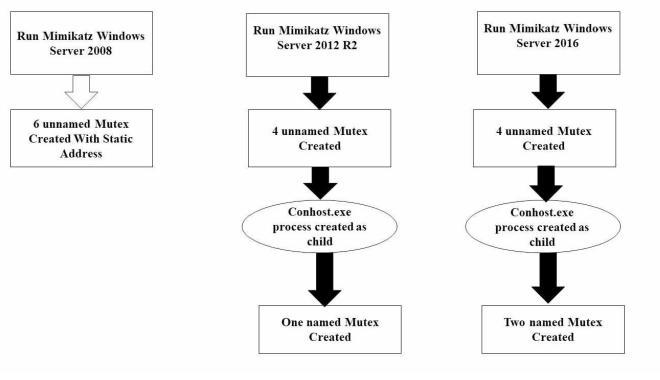
Advanced Persistent Threat (APT) is a stealthy computer network attack. Its threat lies in the fact that unauthorized access to a network is gained and the attackers, whether a person or a group may remain undetected for an extended period. APT group can spread and gain access to the most valuable assets in the targeted organization. Depending on the tools used by APT group it can be hard and complex to respond to those groups and their tools. Mimikatz is one of the most powerful tools used by many APT groups, penetration testers and malware. In this paper, we focus on lateral movement and APT
The Maximum Power Point Tracker (MPPT) provides the most efficient use of a Photo-voltaic system independent of irradiance or temperature fluctuations. This paper introduces the modeling and control of a photo-voltaic system operating at MPPT using the arithmetic optimization algorithm (AOA). The single and double Photo-voltaic models are investigated. Their optimal unknown parameters are extracted using AOA based on commercial Photo-voltaic datasheets. A comparison is performed between these optimal parameters extracted by AOA and other optimization techniques presented in the literature
This paper proposes an algorithm to reconstruct a High Resolution (HR) image from a set of blurred, warped, undersampled, and noisy measured images. The proposed algorithm uses the affine block-based algorithm in the maximum likelihood (ML) estimator. It is tested using synthetic images, where the reconstructed image can be compared with its original. A number of experiments were performed with the proposed algorithm to evaluate its behavior before and after noise addition and also compared with its behavior after noise removal. The proposed system results show that the enhancement factor is
Mobile ad hoc networks heavily rely on nodes' cooperation for packet forwarding. As a result, misbehaving, malicious, and selfish nodes can significantly degrade the performance of the network. To cope with this issue and to stimulate cooperation among selfish mobile nodes, a continuous research effort is done on identifying nodes trust and reputation. In this paper, we survey recently proposed reputation and incentive schemes for ad hoc networks. In order to help in the design of different reputation systems tailored to specific applications and network topologies, we classify the different
Quality of Service (QoS) is one of the major challenges in Mobile Ad-hoc Networks (MANETs), due to their nature and special characteristics. QoS depends on different and multiple metrics such as routing protocols, route stability, channel rate quality, bandwidth, ... etc. Most of studies focus on the above metrics and some of them proposed enhancements. However, there are still unfilled gaps that need to be tackled. In this paper, we focus on the impact of QoS parameters on MANETs. The main objective is to identify the suitable applications in MANETs with respect to the network parameters. ©
Hand gesture recognition is one of the most challenging topics in computer vision. In this paper, a new hand gesture recognition algorithm presenting a 2D representation of histogram of oriented gradients is proposed, where each bin represents a range of angles dealt with in a separate layer which allows using 2DPCA. This method maintains the spatial relation between pixels which enhances the recognition accuracy. In addition, it can be applied on either hand contour or image representing hand details. Experimental results were performed on the latest existing depth camera dataset. The
In this paper, we present an analytical tool for under-standing the performance of structured overlay networks under churn based on the master-equation approach of physics. We motivate and derive an equation for the average number of hops taken by lookups during churn, for the Chord network. We analyse this equation in detail to understand the behaviour with and without churn. We then use this understanding to predict how lookups will scale for varying peer population as well as varying the sizes of the routing tables. We also consider a change in the maintenance algorithm of the overlay, from