
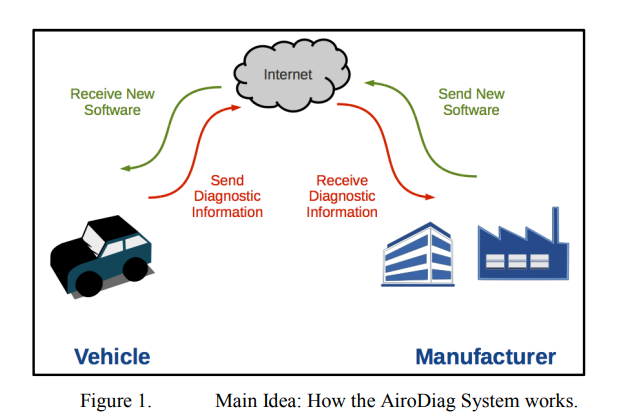
This paper introduces a novel method for diagnosing embedded systems and updating embedded software installed on the electronics control units of vehicles through the Internet using client and server units. It also presents the communication protocols between the vehicle and the manufacturer for instant fault diagnosis and software update while ensuring security for both parties. AiroDiag ensures maximum vehicle efficiency for the driver and provides the manufacturer with up-to-date vehicle performance data, allowing enhanced future software deployment and minimum loss in case of vehicle
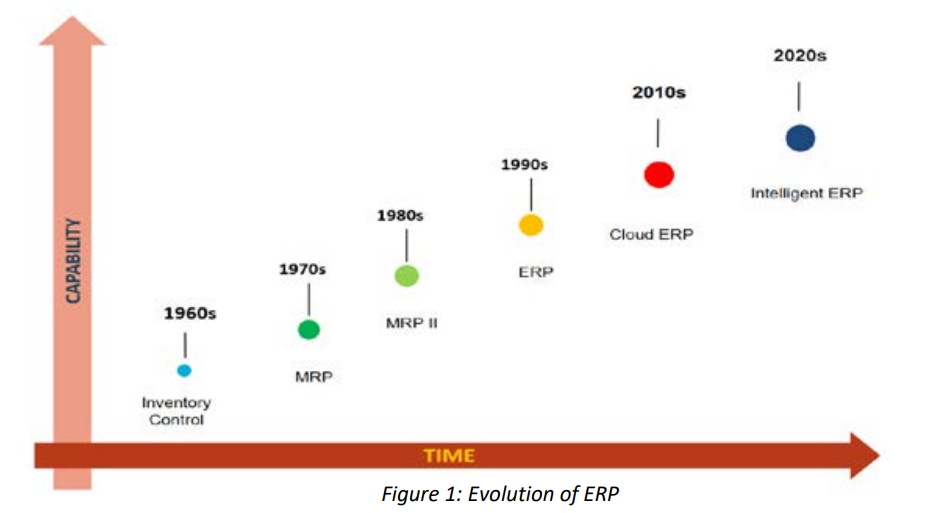
Emerging technologies such as Artificial Intelligence (AI), Blockchain and Internet of Things (IoT) permeate every aspect of work and life. For example, in the supply chain management: IoT-networked sensors can provide real-time insight into the provenance of goods and materials, supplier performance, available capacity, predictive demand and other key data. In turn, this data can feed autonomous and intelligent processes that “learn” how to respond to changing circumstances. Classical ERP systems do not support this distributed innovation. Emerging Technologies in Cloud ERP are what brings
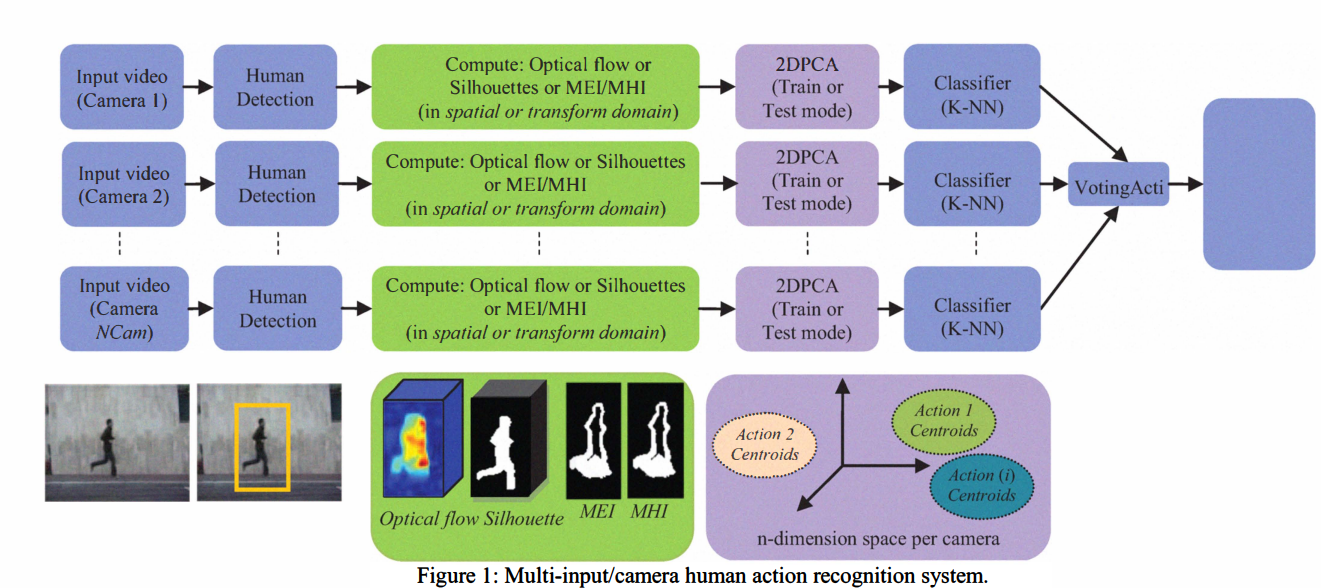
Human action recognition is considered as a challenging problem in the field of computer vision. Most of the reported algorithms are computationally expensive. In this paper, a novel system for human action recognition based on Two-Dimensional Principal Component Analysis (2DPCA) is presented. This method works directly on the optical flow and / or silhouette extracted from the input video in both the spatial domain and the transform domain. The algorithm reduces the computational complexity and storage requirements, while achieving high recognition accuracy, compared with the most recent
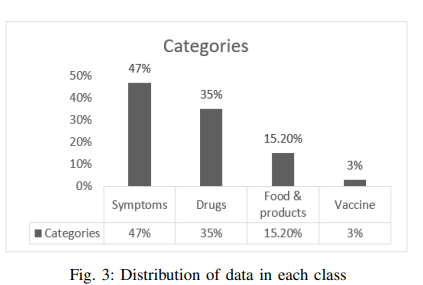
Text classification has been one of the most common natural language processing (NLP) objectives in recent years. Compared to other languages, this mission with Arabic is relatively restricted and in its early stages, and this combination in the medical application area is rare. This paper builds an Arabic health care assistant, specifically a pediatrician that supports Arabic dialects, especially Egyptian accents. The proposed application is a chatbot based on Artificial Intelligence (AI) models after experimenting with Two Bidirectional Encoder Representations from Transformers (BERT) models
SQL injection attacks target databases of web servers. The ability to modify, update, retrieve and delete database contents imposes a high risk on any website in different sectors. In this paper, we investigate the efforts done in the literature to detect and prevent the SQL injection attacks. We also assess the efficiency of the Modsecurity web application firewall in preventing SQL injection attacks. © 2020 IEEE.
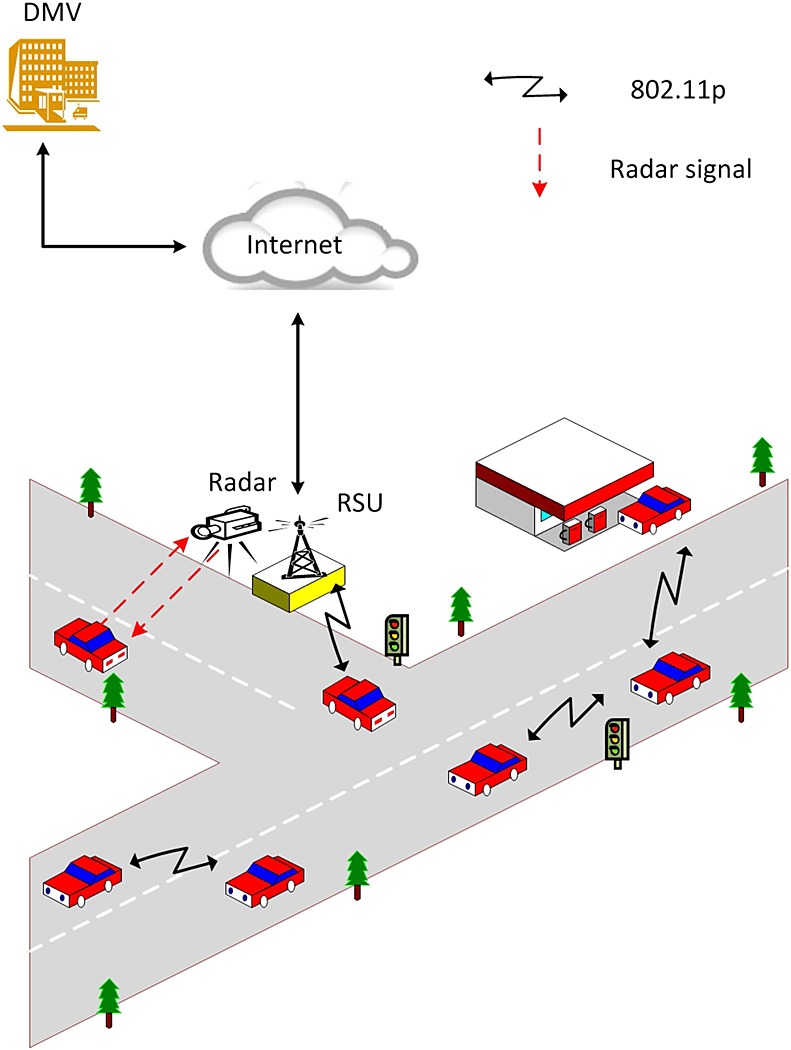
In vehicular ad hoc networks, vehicles should report events to warn the drivers of unexpected hazards on the roads. While these reports can contribute to safer driving, vehicular ad hoc networks suffer from various security threats; a major one is Sybil attacks. In these attacks, an individual attacker can pretend as several vehicles that report a false event. In this paper, we propose a secure event-reporting scheme that is resilient to Sybil attacks and preserves the privacy of drivers. Instead of using asymmetric key cryptography, we use symmetric key cryptography to decrease the
There are many cloud computing initiatives that represent a lot of benefit to enterprise customers. However, there are a lot of challenges and concerns regarding the security and the privacy of the customer data that is hosted on the cloud. We explore in this paper the various aspects of cloud computing regarding data life cycle and its security and privacy challenges along with the devised methodology to address those challenges. We mention some of the regulations and law requirements in place to ensure cloud customer data privacy. © 2017 IEEE.
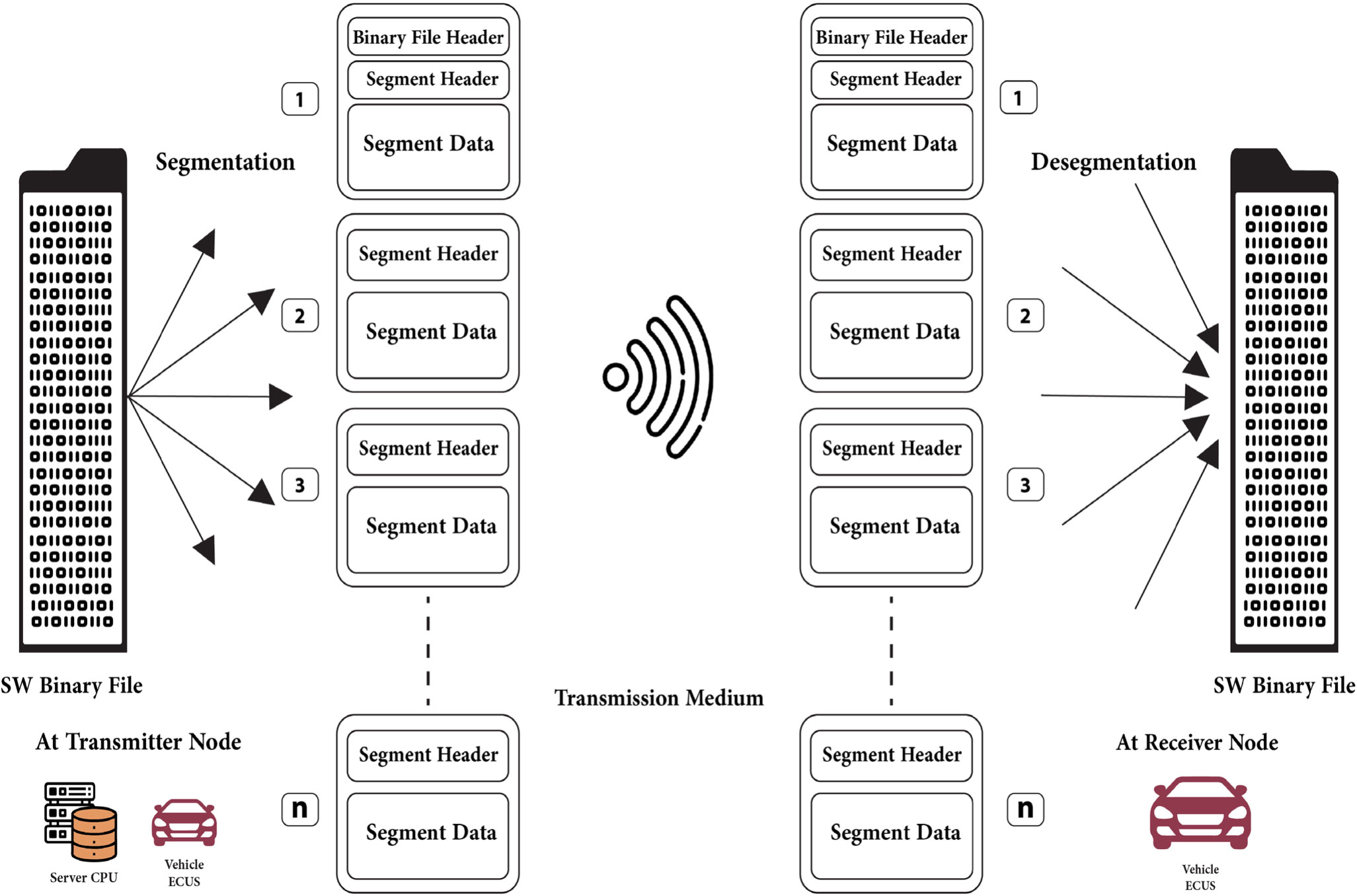
The Internet Protocol (IP) architecture could not fully satisfy the Vehicular Ad-hoc Networks (VANETs) needed efficiency, due to their dynamic topology and high mobility. This paper presents a technique that updates the software of Electronic Control Units (ECUs) in vehicles using segmented Over The Air (OTA) platform over Information-Centric Network (ICN) architecture. In VANET, the amount of time for active vehicles’ connectivity varies due to the vehicular network’s dynamic topologies. The importance of Flashing Over The Air (FOTA) has been illustrated as well as the impact of applying the
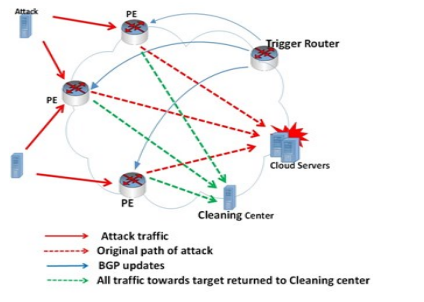
Greater portions of the world are moving to cloud computing because of its advantages However, due to its distributed nature, it can be easily exploited by Distributed Denial of Service (DDoS) attacks. In distributed DDoS attacks, legitimate users are prevented from using cloud resources. In this paper, the various DDoS detection and defenses mechanisms cloud computing are reviewed. We propose a new technique based on Remote Triggered Black Hole (RTBH) to prevent DDoS attacks before it target to cloud resources. © 2018 IEEE.
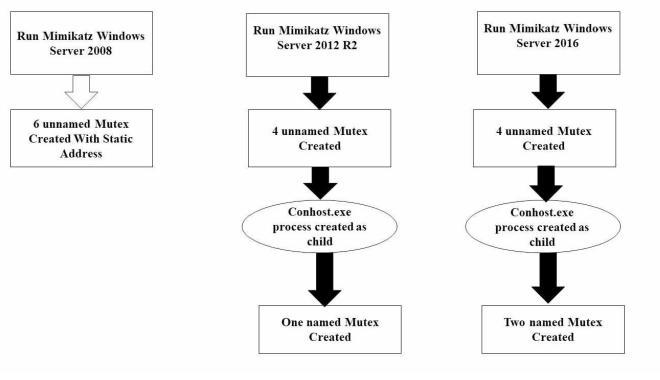
Advanced Persistent Threat (APT) is a stealthy computer network attack. Its threat lies in the fact that unauthorized access to a network is gained and the attackers, whether a person or a group may remain undetected for an extended period. APT group can spread and gain access to the most valuable assets in the targeted organization. Depending on the tools used by APT group it can be hard and complex to respond to those groups and their tools. Mimikatz is one of the most powerful tools used by many APT groups, penetration testers and malware. In this paper, we focus on lateral movement and APT