
Artificial Intelligence
Evaluation of the performance of a FONN-based MPPT control for a photovoltaic watering system
This study aims to increase the effectiveness of photovoltaic pumping systems. A practical installation and cost-effective design are suggested. This paper examines the nonlinear behaviour of photovoltaic generators from a distinct perspective; where it repeatedly transitions between a constant current and a constant voltage source and shows how this affects the behaviour of the induction motors. A Fractional-order Neural Network (FONN) is suggested to forecast the harvested solar-energy. The results showed that FONN improved forecasting accuracy by effectively capturing the nonlinear
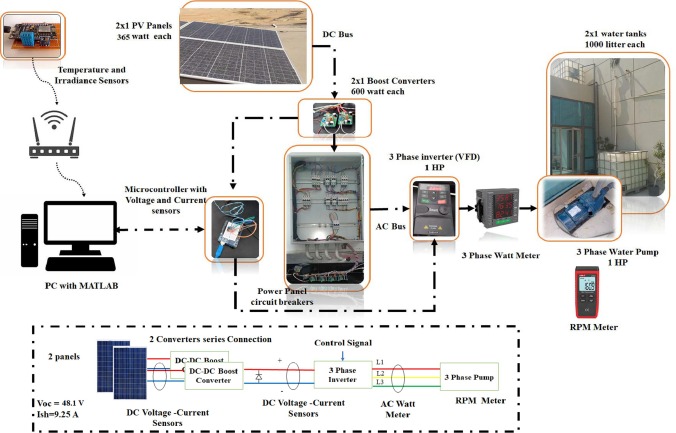
Optimal fractional-order fuzzy-MPPT for solar water pumping system
This paper seeks to improve the efficiency of photovoltaic (PV) water pumping system using Fractional-order Fuzzy Maximum Power Point Tracking (FoF-MPPT) control and Gray Wolf Optimization (GWO) technique. The fractional calculus has been used to provide an enhanced model of PV water pumping system to, accurately, describe its nonlinear characteristics. Moreover, three metaheuristic optimizers are applied to tune the parameters of the proposed FoF-MPPT, Particle Swarm Optimization (PSO), Ant Colony Optimization (ACO) and the GWO. The FoF-MPPT is intensively tested and compared to the Perturb
An Efficient Design and Control Techniques of Photo-Voltaic Pumping System (PVPS)
In this paper, new methods for increasing the efficiency of photovoltaic pumping systems are presented (PVPS). A feasible implementation of battery-free PVPS, as well as a cost-effective design, has been proposed. The variation of the PV power causes its behaviour to transit permanently between the characteristics of constant current sources and constant voltage sources, which is studied in this paper from a new perspective. The inconsistency of PV generator behaviour reveals an unexpected phenomenon in the operation of induction motors (IM). To overcome the effects of fluctuating PV behaviour

Analytical solution for the quasi-two dimensional non-isothermal fully developed flow of molten salt in a circular pipe
In this contribution, a mathematical model is presented for the flow of molten salt in a circular pipe. The fluid density, thermal conductivity, and viscosity are all assumed to be temperature dependent. We show how to derive a new closed-form approximate solution to this problem, valid for low Reynolds numbers and high axial temperature gradients. This regime is chosen to challenge the ability of the model to obtain the correct solution for significant changes in fluid properties. The accuracy of this simplified solution is tested against a numerical solution of the full set of governing
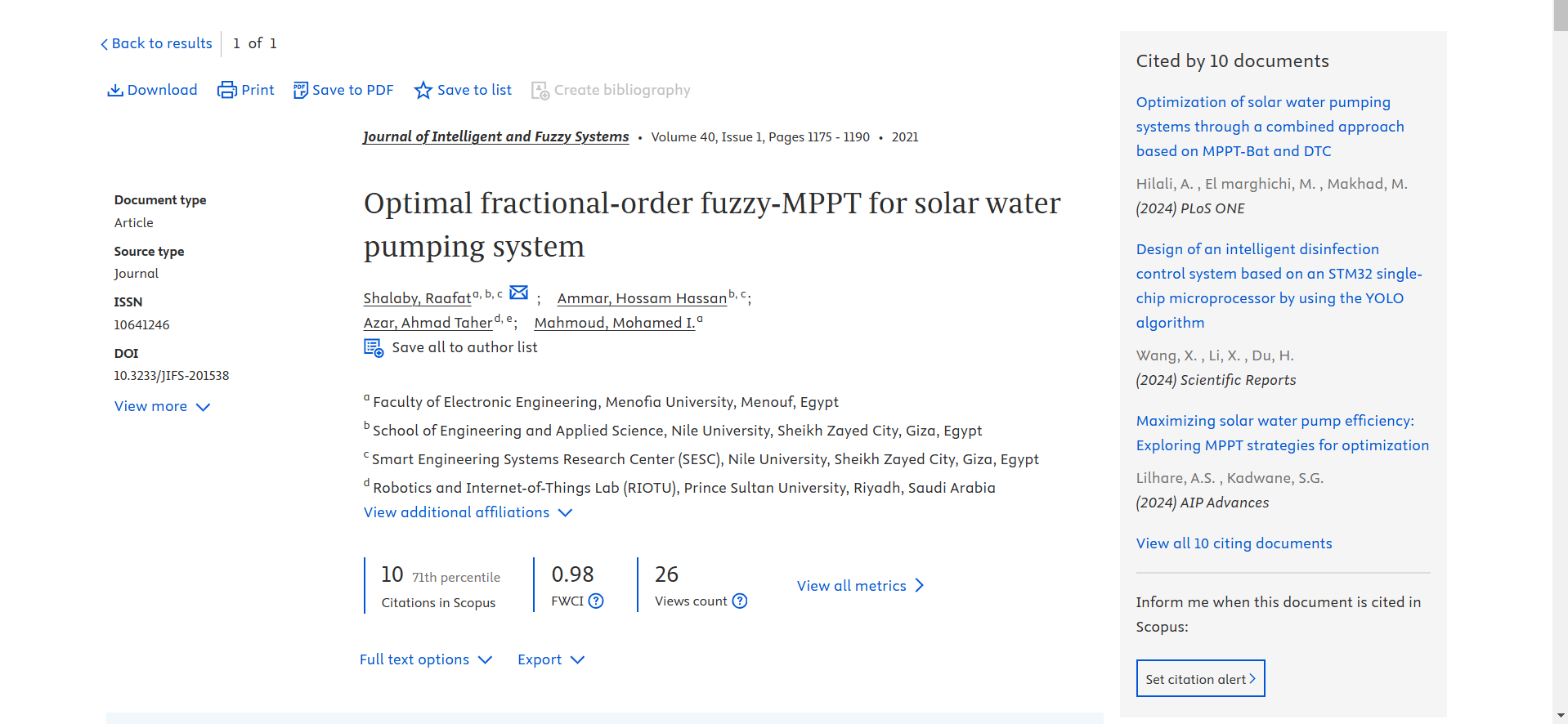
Nonlinear analysis of Euler beams resting on a tensionless soil with arbitrary configurations
Background: The nonlinear interaction between an elastic Euler beam and a tensionless soil foundation is studied. The exact analytical solutions of the nonlinear problem are rather complicated. The main difficulty is imposing compatibility conditions at lift-off points. These points are determined as a part of the solution, although being needed to get the solution itself. In the current work, semi-analytical solutions are derived using the Rayleigh–Ritz method. The principle of vanishing variation of potential energy is adopted. The solution is approximated using a set of suitable trial
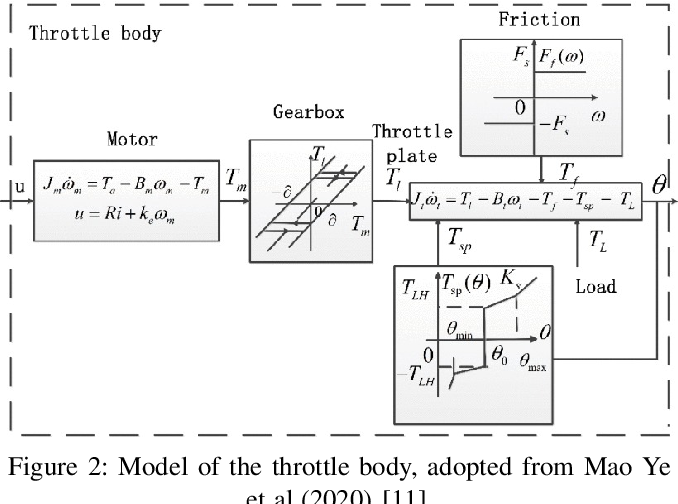
Optimizing Automotive Electronic Throttle Control with a Modified Grey Wolf Algorithm
Electronic Throttle Control (ETC) systems have become increasingly popular in the automotive industry due to their ability to improve fuel efficiency and vehicle performance. However, designing effective control strategies for these systems is challenging due to the non-linearities and external load affecting the throttle gate angle. This paper proposes a novel control approach for ETC systems using a modified Grey Wolf optimization algorithm combined with a fractional-order PID controller. The proposed approach is designed to handle the tuning of the controller's five parameters in the
Optimization of solar tree performance in Egypt: a simulation-based investigation
The paper discusses the orientation and positions of solar panels in a solar tree. Solar energy contributes to the most available and abundant energy source in Egypt. Hence, The PV system is considered a promising solution to generate power from this source. However, its energy density is low. Therefore, the solar tree is considered in this paper as it has higher density and fits the urban cities of Egypt. The design of the solar tree is divided into two sections: the study of the solar panel’s orientation and positions. For the solar tree orientation, a single-objective genetic algorithm is
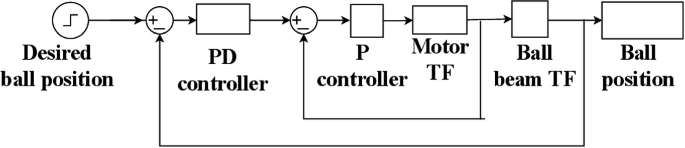
Optimal PD-PD and State Feedback Control of Underactuated Ball and Beam System with Uncertainty and Disturbances
This research paper investigates the optimal control of the ball and beam system, a challenging fourth-degree system that is commonly used in control studies. Four different control techniques, namely cascaded PD-P, cascaded PD-PD, optimized cascaded PD-PD control using a genetic algorithm, and state feedback control, are compared in terms of their performance. The study aims to achieve specific design criteria, including low rise time, less than three percent overshoot, and less than two seconds of settling time. In addition, the impact of disturbances, uncertainty, control action, and beam
Path Planning of a Self Driving Vehicle Using Artificial Intelligence Techniques and Machine Vision
This paper aims to implement an efficient model of the most optimum path to follow an object on a Self Driving Vehicle (SDV). The path of the vehicle is predicted by using Machine Vision (MV) and Neural networks (NN) model. The NN model uses numerous amounts of training data. First the system works by using the MV algorithms to detect objects with predefined colors. Then, the location of the object is fed to the trained NN to get the speeds of the motors needed to reach the object. The training data are obtained from the manual driving of the vehicle in different experiment settings. In this
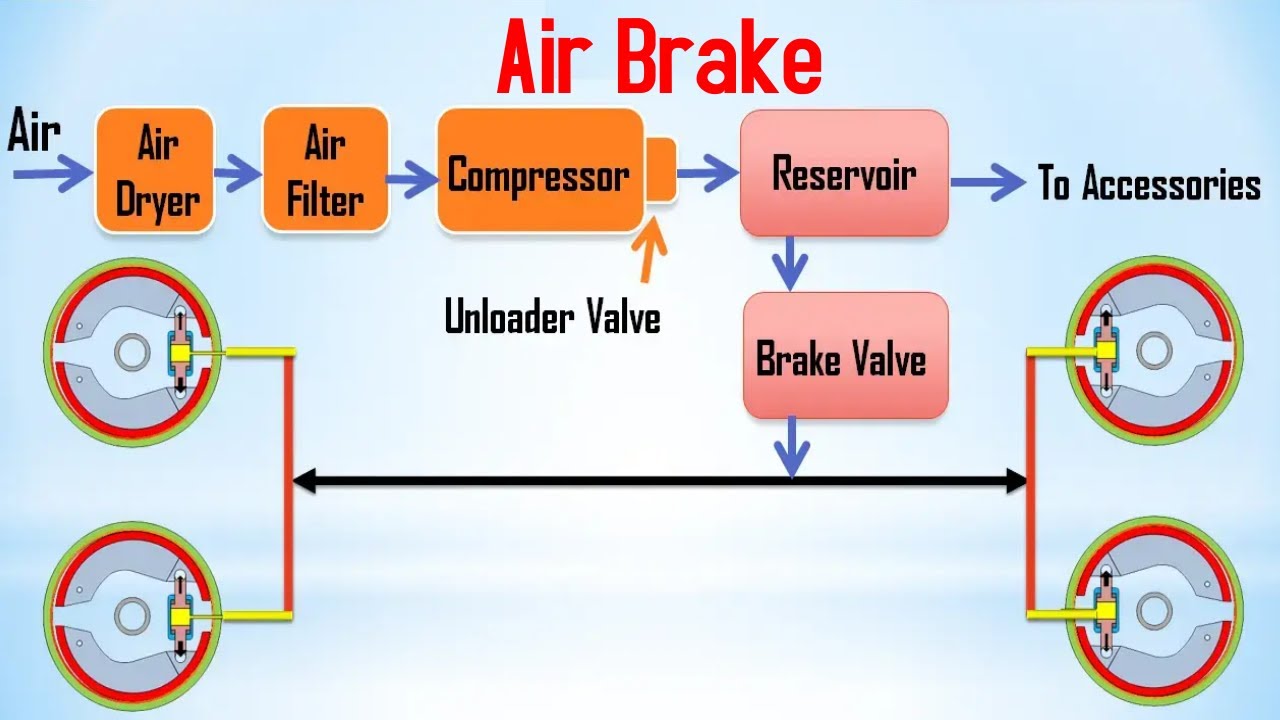
Thermal Air Braking
This paper introduces the concept of thermal air braking, which involves heating a portion of the airfoil's upper surface to achieve the braking effect. A 2D Computational Fluid Dynamics (CFD) analysis is conducted using ANSYS Fluent software to study the impact of heating the upper back portion of the top surface of an airfoil. The study compares the results of the heated and non-heated cases for NACA 4415. Different aerodynamic efficiencies are investigated, such as lift coefficient (CL), drag coefficient (CD), lift-to-drag coefficient (CL/CD), and pressure coefficient (CP). The results are


